Features.
ZITADEL as identity experience platform provides all the features for identity management, secure authentication, and access management for your customers, employees, devices or services. Our platform makes it easy to deploy a hosted, multi-factor secured login, offer single sign-on, allow users to bring existing identities, integrate with our APIs, and keep informed with our event-based audit trail.
Delegated Access Management
ZITADEL lets you delegate the access management between organizations.

Delegated access management means you can select a subset of roles for a given project and allow the granted organization to self-manage those roles for their users. Delegation is a highly useful feature for SaaS companies that have some sort of organization as customers, for example a B2B software provider. The SaaS provider wants to delegate the ability to manage access for certain roles of my service to customers or partners.
Hosted Login
Easily authenticate your users with a customizable hosted login page.
Welcome back
john@example.com
Let us take out the pain of running a secure login and register page for your projects. Use the convenience of a single sign-on (SSO) solution to login with every possible service. ZITADEL enables SSO via standard protocols such as OpenID Connect.
Use your brand
Let your audience recognize your brand with our customization options. These include custom logos, colors, fonts and event texts for the login page and emails as well. You can do this in our management interface without touching any code, and preview your login before deploying to the live version to customers.
Gain control over your users authentication
Let your audience recognize your brand with our customization options. These include custom logos, colors, fonts and event texts for the login page and emails as well. You can do this in our management interface without touching any code, and preview your login before deploying to the live version to customers.
Multifactor Authentication
Don't give passwords like
any chance and secure access with multiple factors.
Protecting user accounts with only a password is not secure anymore. Some countries and industries already require companies to enforce strong authentication with a second factor. Our various multifactor authentication methods enable you to better protect users and their data. For an even better user experience and higher security, we recommend using passwordless authentication.
Login
John logs in with his username and password.
Second Factor
John scans his finger as second factor to complete the login.
Authenticated
John uses all allowed apps without being asked to login in again.
No extra charge
Do you want to improve your security and at the same time improve the usability? Simply use ZITADEL as your solution for secure authentication. We don’t charge you extra for things like multifactor (MFA) and second factor (2FA) authentication capabilities, which should be default in a modern IAM solution
Enforce security with policies
Do you want to tighten security for your organization? Define policies for your organization to control what MFA and 2FA options are available to your users. For example you can create a policy to enforce login with only passworless methods, improving user experience while reducing attack surface for phishing.
Passwordless
Replace passwords with a phishing resistant and convenient authentication with Passkeys.
Instead of typing your password and entering a second factor, ZITADEL requests your fingerprint, security key, or any other WebAuthN compatible authentication method on your device to login. Authentication with Passkeys is based on the open standard FIDO2 and protects users effectively against phishing, thus eliminating a major attack vector of passwords.
Be part of the Passkey future
Users don't have to remember complex passwords, or need to search for a second factor code, greatly improving user experience. Instead they will get to login faster, with a more secure and easier login experience. FIDO2 is backed by leading software providers and developers of consumer devices
Audit Trail
Security incidents are often detected too late, when log files are already deleted or out of context. Our solution provides you with a builtin audit trail that tracks all changes over an unlimited period of time.
When information is updated, other solutions replace the historic record and track changes in separate logs. Our solution only appends data in an event store, keeping all historic records. This gives you the opportunity to review records way in the past and for us ideal data for advanced threat analytics to keep your users safe.
Travel back in time
With our unique way of storing data we can show you all of your resources at a given point in time. Inspect how a user looked three months ago compared to now or what roles a project contained in the past.
Identity Brokering
Users can use external identity providers to login to your connected applications.
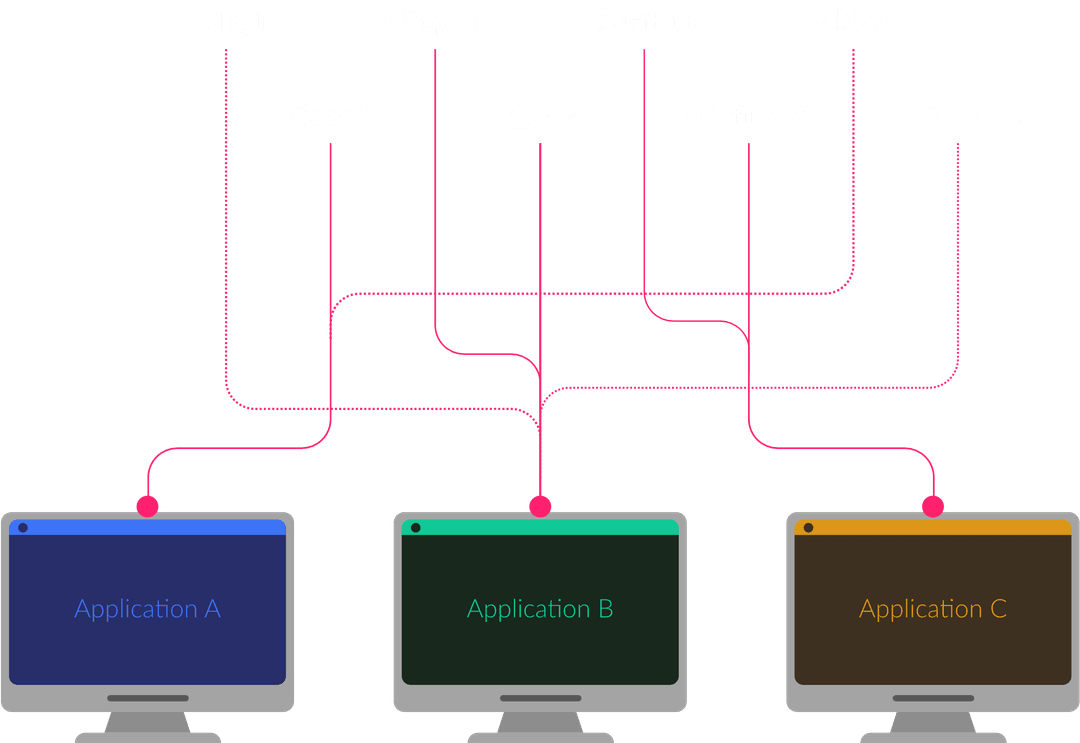
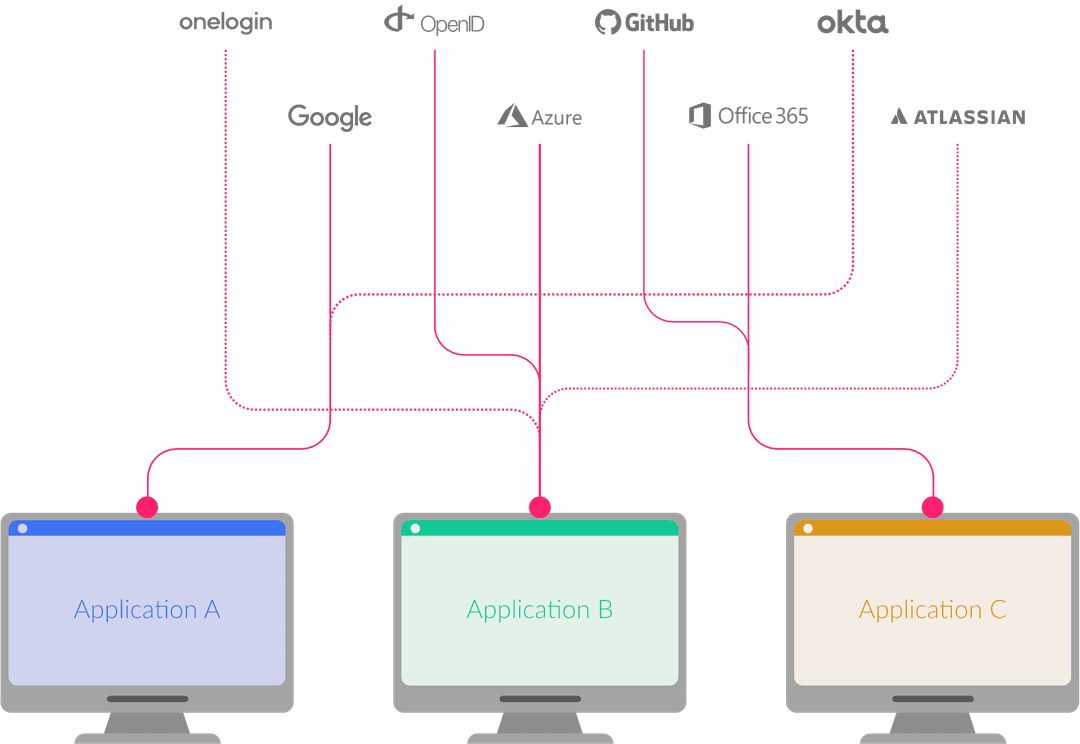
Integrating multiple Identity Providers directly within your applications is complex to maintain, costs time to setup, and hinders single-sign-on of users - simply, it does not scale. As identity broker, ZITADEL acts as trusted intermediary service connecting your projects with different identity providers. A user can self-manage identity brokering and link multiple external identity providers to his identity.
Let customers reuse existing identities
Enable your customers, employees, or business partners to user their existing identities and identity providers with your application.
Social and Government IDs
Allow your customers to reuse their social or government identities to register or login with your application.
Enterprise IDs
Enable customers to self-manage their organization's federation setup. Our management interface provides a unique self-service option for your business customers requiring federation with systems like, Keycloak, Auth0, AzureAD.
Rely on a robust trust anchor
Integrate with ZITADEL using well established protocols like OpenID Connect and OAuth 2.0 and broker all external IDPs. Don't integrate each application individually and don't bother with special protocols of the providers. Simply rely on the identity provided by ZITADEL, a robust trust anchor for all your applications and devices.
Ease your access management pain
Assign roles to brokered identities, like you do with any other user, and rely on a robust access management process that is highly reproducible for your application.
Platform APIs
ZITADEL is built around the idea of easy integration.

Multiple parties can integrate custom use-cases for digital identities on top of solid core features. To enable easy integration into your business case, nearly all functions can be accessed via an API. With this we achieve a proper separation of concern and don’t need to integrate custom code within our codebase.
Manage all resources
Most important for integrators is the Management API: It provides all features to manage Organizations, Users, and Projects. Furthermore, you can use our IAM API to configure the whole IAM system. Authentication and user information can be accessed through the Authentication API.
Machine to Machine communication
ZITADEL simplifies authentication and integration with your non-interactive applications or devices.
ZITADEL offers multiple options for third party applications or devices to connect and allows you to tailor access rights to your use cases.
CLIs
Use authentication for your command-line interface to build seemlessly integrated tools.

