Zitadel vs Auth0: The Definitive Comparison for Enterprise Identity Infrastructure

Product Marketing
- Introduction: Auth0 (by Okta) and Zitadel
When choosing the right authentication provider for your application it can be hard to narrow down one that works not just for your organization internally but also for your customer and partners. Recognizing the diverse needs of a modern identity management system that is both flexible and secure can become an overwhelming task, especially in a market that offers a plethora of alternatives. That’s why it is important to understand the value proposition of the vendor offerings and evaluate how they fit your organizational requirements.
In this article, we will do a quick comparison of the two alternatives - Auth0 by Okta and Zitadel.
Introduction: Auth0 (by Okta) and Zitadel
Auth0 by Okta
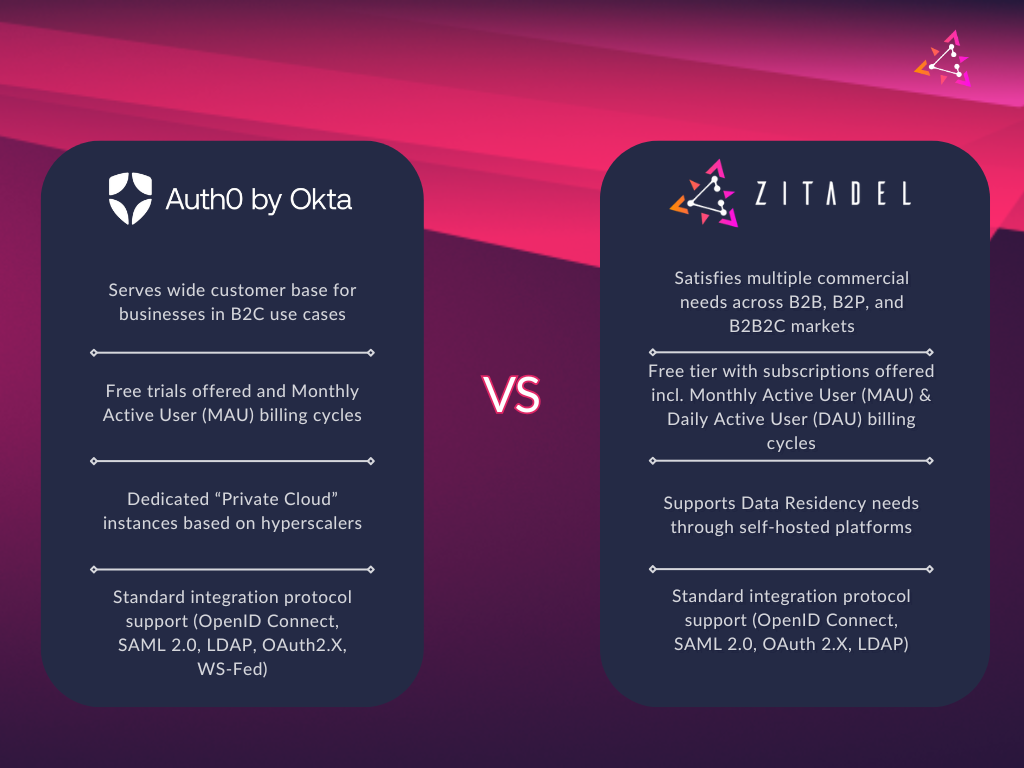
Auth0 by Okta (referred to as Auth0 in the rest of the article), is a well-reputed Identity and Access Management solution. It historically has had a strong developer focus and supports a variety of use-cases and integrations. Auth0 is a pure SaaS-oriented, closed-source platform. You have the option to get dedicated setups referred to as "private cloud" that reside on popular hyperscalers. The pricing is oriented around tiers and monthly active users with a free tier for small scale developer projects. Auth0 supports the standard integration protocols like OpenID Connect, SAML 2.0 and WS-Fed.
Zitadel
Zitadel is an API-first identity platform that is built for developers. It offers easier integration into your tech stack to support the authentication, authorization, and self-service needs. Offered as an open source and a commercial solution, it also provides a long-term audit trail out-of-the-box to ensure the security and compliance posture for your organization. Zitadel is offered in free and cloud subscription tiers, along with a self-hosted version for organizations that require complete data ownership. Zitadel’s comprehensive identity platform supports business-to-business (B2B) use cases including multi-tenancy, identity brokering, multi-factor or passwordless authentication, delegated access management, and in-context audit trail. Zitadel supports the standard integration protocols such as OpenID Connect, SAML 2.0, and OAuth 2.0.
Core Differences
Source Code
Auth0 and Zitadel have quite a big difference in regard to their position of publicizing their source code. Auth0 is closed source project and Zitadel is an open source project. Up to version 2, Zitadel leveraged the Apache 2.0 license but will transition to the GNU Affero General Public License v3.0 (AGPL-3.0) with the upcoming version 3. The AGPL license ensures that any modifications to Zitadel need to be made available to the community. This creates a more reciprocal relationship between Zitadel and organizations that leverage and build upon our platform. It protects the open nature of our project while encouraging contributions back to the community.
For most of Zitadel’s community, this change will have minimal impact:
For end-users: If you are only using Zitadel as an identity platform, the license change doesn't affect you. For contributors: Your future contributions will be licensed under AGPL-3.0 and we will introduce a contributor license agreement (CLA). For service providers: If you modify Zitadel and provide it as a service to others, you'll need to make your modifications available under the AGPL-3.0 license. For developers: If you are using our Examples, Libraries, SDKs, APIs, do not worry we will keep those under their existing license.
Our commercial licensing options remain available for organizations that require different terms. Please reach out to us if you have any questions about licensing, we have compiled a detailed blog post and an FAQ for you.
Operating Model
While Auth0 operates in a SaaS model with the option to get a private cloud system on one of the well-known hyperscalers, Zitadel operates under an Open SaaS ideology (SaaS built with OSS). As an open-source solution, Zitadel can be self-hosted, giving organizations complete control over their data and infrastructure. Zitadel also offers the ability to run a dedicated instance or support to our customers who are in need to self host. If you are trying to decide between cloud or self-hosting, we recently wrote a blog post laying out the pros and cons of self-hosting and a cloud approach.
Pricing
Auth0 offers by default a “Monthly Active User” pricing strategy. A common frustration for customers is that Auth0 bases its billing on peak usage rather than actual real-time consumption, which usually results in unanticipated costs. This, in combination with the need to pay extra for security features like multi-factor authentication makes it a costlier option. The user-based pricing offers an easier starting point but the fact that critical security features are only available in higher tiers hides the true cost for production-ready scenarios.
Zitadel’s pricing model is tailored to your organization’s needs, focusing on three core elements: Support Level Agreements (SLA), Daily Active Users (DAUs), and Technical Account Management (TAM). We include essential features such as multifactor authentication and passkeys at no additional cost, and we don’t charge based on the total number of users stored in your system.
Project Structure
Zitadel has a unique way to group clients that belong to the same security context into what we call “Project”. Projects help users bundle together clients, for example a web-application and a mobile-application, that share the same authorization mechanics. This ensures developers see consistent results across all clients without needing to manually configure audience scopes. The project allows you to delegate the access control and permission management to a third party. More details on how our “project grants” work are here.
Auth0 currently lacks functionality to manage applications as a cohesive group.
Self Service
While Auth0 provides authentication interfaces for sign-up, login and password reset, it lacks broader self-service capabilities such as user profile page or ability to manage users as business partners. In contrast, Zitadel offers comprehensive self-service capabilities including user profile management, access control delegation, and the ability for business customers to configure their own identity providers.
Data Residency
When creating an Auth0 tenant, you must select one of four geographic regions for data storage: US, Europe, Japan, or Australia. Auth0’s region selection is not easily modifiable after initial setup, and this single-region architecture may increase latency for customers accessing services from other geographic regions.
Zitadel offers flexible data residency options with hosting regions the United States, Europe, Switzerland, or Australia. Organizations can deploy multiple instances across different regions to optimize global coverage. For strict data residency requirements, Zitadel supports regional cloud hosting and self-hosted deployments, giving organizations complete control over their data location and security protocols. Many of our enterprise customers choose self-hosted deployments to maintain maximum control over their infrastructure and data governance.
Location of Incorporation
Auth0, incorporated in the United States, was acquired in 2021 by Okta which is also incorporated in the United States. With headquarters in the United States and a principal office in Switzerland, Zitadel provides flexible contracting options through its dual-entity structure. Organizations serving European Union customers can contract through Zitadel's Swiss entity, leveraging Switzerland's data protection adequacy status granted by the European Commission. This simplifies EU data transfer compliance compared to the more complex requirements for US-based providers.
Extensibility
Zitadel and Auth0 both have Actions to support extensibility through debugging and logging capabilities. Zitadel’s event-driven architecture enables organizations to customize workflows by responding to any authentication or audit event. The Zitadel platform’s Session API and Login Experience features offer extensive customization options for both functionality and branding to align with your organization’s requirements. As a fast-growing open-source company, Zitadel rapidly incorporates customer feedback through strategic partnerships and contributions on GitHub.
What’s Next for Zitadel: Development Priorities for 2025
Zitadel maintains a public product roadmap and operates with full transparency as an open-source platform. It includes significant feature releases planned for platform development and performance optimization in 2025.
Performance Optimization:
Comprehensive platform-wide performance enhancements that focus on core authentication service response times, API endpoint optimization across new and existing services, enhanced resource management efficiency, and improved system scalability.
TypeScript Login with OIDC:
A new, highly customizable login interface for our customers, built in with TypeScript and OpenID Connect support. Self-hosting customers will soon be able to use the hosted login option with OIDC.
User Schema Management:
This feature offers advanced user profile customization enabling granular control over field management permissions between users and administrators.
Configurable Caching System:
Beta release of flexible caching infrastructure supporting Redis integration for improved object lookup performance.
SCIM Integration:
This is the implementation of System for Cross-domain Identity Management (SCIM) protocol for automated user provisioning, synchronization, and lifecycle management across external systems.
Actions Framework v2:
This feature offers enhanced extensibility framework supporting custom triggers and executions through API endpoints for advanced workflow customization.
User Group Authorization:
The implementation of user group management capabilities enable efficient authorization management at scale, expanding beyond individual user permissions.
Decision Framework:
Zitadel is particularly suitable for organizations that prioritize these capabilities:
Security and Control:
Your organization requires complete control over infrastructure through self-hosting options, and you need robust data protection measures. Zitadel’s comprehensive audit trails provide detailed long-term tracking of all authentication and authorization activities.
Business Architecture:
Zitadel excels in multi-tenant environments, making it ideal for organizations managing multiple client organizations or separate business units. Zitadel’s B2B-focused approach is designed to handle complex organizational relationships and hierarchies.
Technology Philosophy:
If your organization values open-source solutions, Zitadel offers full transparency and the ability to customize the platform to your needs. It is built on cloud-native and serverless principles, making it a natural fit for modern, scalable architectures.
Community Engagement:
As an open-source platform, Zitadel welcomes direct contributions from its user community. This means you can actively participate in improving the platform and adapting it to meet emerging needs in identity management.
Take Control of your Identity Infrastructure
Transform your organization’s identity, authentication, and access control with Zitadel. Connect with our team to:
- Assess your current identity infrastructure needs
- Design a tailored implementation strategy
- Learn how to scale seamlessly as your organization grows
Book a consultation today to start your journey towards simplified, secure identity management.
Please share your feedback to ensure this guide remains accurate and valuable for the community. Your insights help us maintain the quality and relevance of our documentation.